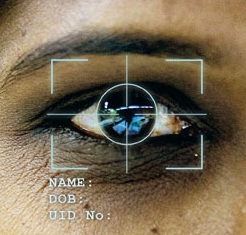
 Remember the old ad line, “Sell the sizzle, not the steak” ? There seems to be a lot of that going on with biometric systems. There’s all kinds of excitement about what new body part can be quantified and its near-holy-grail-ness for authentication (the sizzle), but not a lot of talk about the infrastructure required (the steak) to provide the sizzle. By default, the cost of the steak falls back to the customer, the implementer of the biometrics system.
Remember the old ad line, “Sell the sizzle, not the steak” ? There seems to be a lot of that going on with biometric systems. There’s all kinds of excitement about what new body part can be quantified and its near-holy-grail-ness for authentication (the sizzle), but not a lot of talk about the infrastructure required (the steak) to provide the sizzle. By default, the cost of the steak falls back to the customer, the implementer of the biometrics system.
Interest in biometrics systems for authentication — sensing fingerprints, iris scanning, voice, other — continues to accelerate for several reasons:
- recognition of inadequacy of passwords as sole system for authentication
- increasingly hostile online world — cybercrime, nation-state actors, civil unrest
- rise of the Internet of Things — rapidly increasing ability to manufacture and deploy inexpensive, microcontrolled, networked sensors
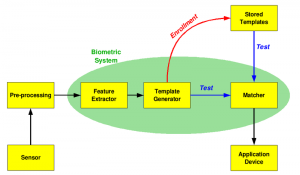
Image: WikiCommons
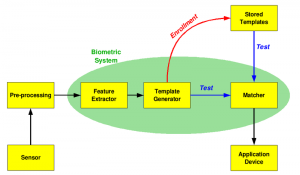
Complex Subsystems
Biometrics systems require several functional, secure, and integrated components to work properly with appropriate privacy requirements in mind. They need a template to structure and store the biometric data, secure transmission and storage capabilities, enrollment processes, authentication processes, and other components. These backend systems and processes, the steak, can be large, complex, and require real oversight and resources. For example, the enrollment process (getting someone’s biometric profile, aka template, into the database involves multiple, if quick, phases — sensing, pre-processing, feature extraction, template generation, etc.)
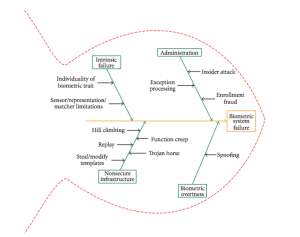
Like all systems, there are many points of attack or places where the system has some vulnerabilities as indicated in this vulnerability diagram in a paper by Jain, et al in this article.
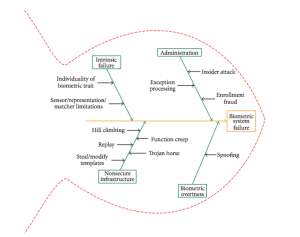
Biometric Template Security. Jain, Nandakumar, Nagar.
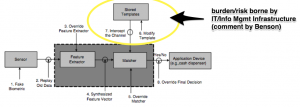
Uncaptured Cost of Infrastructure Enhancement
While there are many points of failure (again as in all systems), the infrastructure component lies squarely with the customer. Its cost will show up as required enhancements, resources, and staffing to support the additional required infrastructure or it will show up as the cost of unmitigated risk.
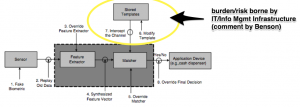
Biometric Template Security: Challenges & Solutions. Jain, Ross, Uludag. (comment by author) http://bit.ly/1fWC21i
The infrastructure cost (or cost of unmitigated risk) occurs because the user’s biometric profile has to be stored somewhere and has to be transmitted to that somewhere and all the other things that we sometimes do with data — backup locally, backup at a distance, audit, maybe validate, etc. That profile data is the data that is used for comparison for a new real-time scan when someone is trying to unlock a door, for example. It is the reference point.
Because biometric data is about as personal as you can get, way more personal than a Social Security Number or credit card number — you can change those after all — that personal profile data needs to be highly protected. So that means that, at a minimum, you’ll probably want to store the profile encrypted and also transmit the data in encrypted sessions. That’s generally an IT infrastructure function, not a biometric device function.
Some questions to ask your vendor
When considering purchase of a biometric system, a partial list of things to consider might include:
- How is the biometric profile data (a parameterized fingerprint, for example) exchanged between the sensing/scanning device and the database that stores the parameter? Is it encrypted? If encrypted, how is it encrypted? Protocols?
- Is biometric profile data cached on the device either at time of enrollment or actual use? If so, how long? While cached, is it encrypted?
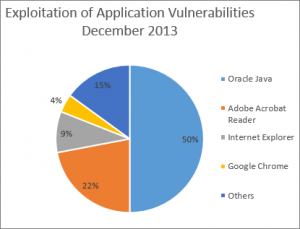
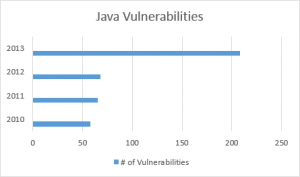
- Does the system use 3rd party software anywhere in the chain, eg device configuration via web service? If so, who wrote it? What is their reputation?
- Does the device manufacturer publish data on the current chip set? Chip manufacturer, version, when purchased, etc?
- How long does the enrollment process take?
- What is the scope of the install? Door entry? Computer access? Other?
- Are there other installations? Case histories of user adoption?
- Are there auditing, logging, reporting functions from the system?
Whether the biometric system includes just the sensing endpoint device or has backend support to include database and application support, it is critical that the customer knows where the biometric system infrastructure ends and where their own infrastructure begins and has to carry the burden of the new biometric system implementation.
To ensure privacy and security, someone has to pay for the steak that provides the sizzle. It’s best to figure that out who’s going to do that ahead of time.
Other reading:
[Eye Image: licensed under the Creative Commons Attribution-Share Alike 3.0 Unported license.