 A team of researchers has identified a way to extract full 4096-bit RSA decryption keys just by listening to (detecting) the sounds generated by a computer. Sound patterns can be associated with particular processes occurring on the computer. Of special interest are the unique sound patterns generated when cyphertext (text that has been encrypted) is in the process of being decrypted. The researchers claim that in less than an hour a decryption key can be identified by analyzing sound patterns generated by decryption of particular cyphertexts. Interestingly, this is not sound generated by fans, hard drives, or speakers, but rather sound generated by electronic components such as inductors and capacitors.
A team of researchers has identified a way to extract full 4096-bit RSA decryption keys just by listening to (detecting) the sounds generated by a computer. Sound patterns can be associated with particular processes occurring on the computer. Of special interest are the unique sound patterns generated when cyphertext (text that has been encrypted) is in the process of being decrypted. The researchers claim that in less than an hour a decryption key can be identified by analyzing sound patterns generated by decryption of particular cyphertexts. Interestingly, this is not sound generated by fans, hard drives, or speakers, but rather sound generated by electronic components such as inductors and capacitors.
Handling interference
Most of the information-yielding acoustics occur above the 10 KHz range. Fan noise and typical room noise generally occurs at lower frequencies and can be filtered out.
Depending on the environment, some keys can be decrypted by using a smart phone within approximately 30 cm. Ranges of up to 4 meters have been successful using specialized equipment such as parabolic microphones.
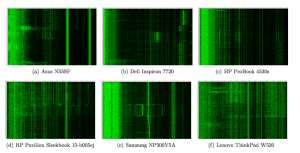
Different computers have different signatures, but distinct core computing operations such as the HLT (cpu sleep), MUL (integer multiplication), & FMUL (floating point multiplication) X86 instructions can be identified in each.
“Magic-touch” attack
Another variant is what the authors call a magic-touch attack. In this scenario, instead of detecting patterns in sound coming from the computer, variations in ground potential of the device can be analyzed. As with the acoustic analysis, these voltage variations in the device’s ground can be also be correlated to specific processing patterns. These ground-potential changes can be measured directly or even by simply touching the chassis with one’s hand and then measuring the variation in body potential. Another approach is to measure the ground potential on the far side of a cable that has a ground, such as a VGA cable.
I think the genie has escaped …
